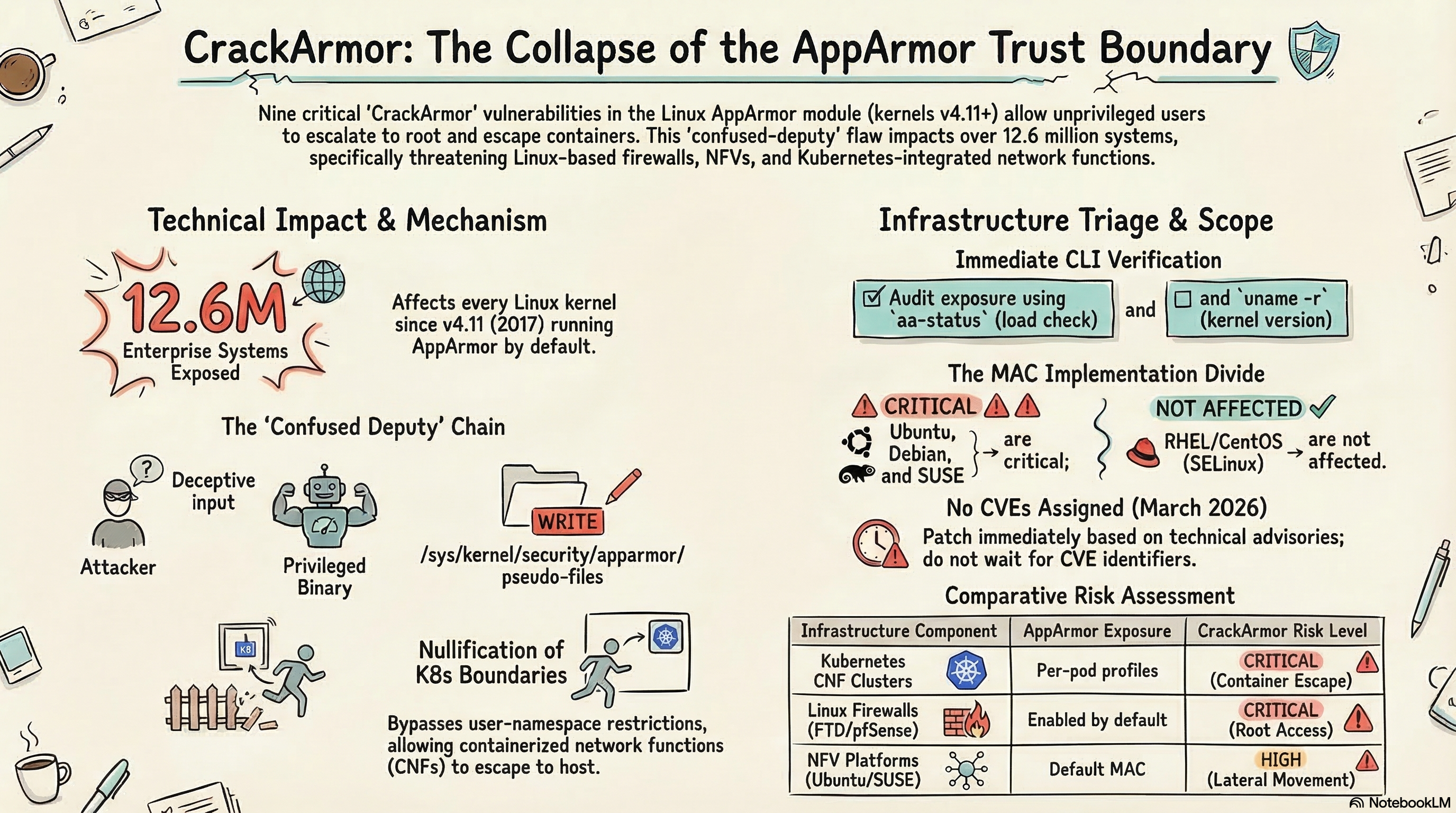
Nine critical vulnerabilities in Linux AppArmor — collectively dubbed “CrackArmor” by the Qualys Threat Research Unit — allow any unprivileged local user to escalate privileges to root, break container isolation, and crash entire systems. According to Qualys (2026), over 12.6 million enterprise Linux instances run with AppArmor enabled by default, and these flaws have existed since kernel v4.11, released in April 2017. If you run network infrastructure on Ubuntu, Debian, or SUSE — and statistically, many of your appliances do — this is a patch-now situation.
Key Takeaway: CrackArmor collapses the trust boundary that AppArmor provides for containers, network functions, and security appliances. Any Linux-based network device running an affected kernel needs immediate patching — before an unprivileged user turns a container escape into full infrastructure compromise.

What Exactly Are the CrackArmor Vulnerabilities?
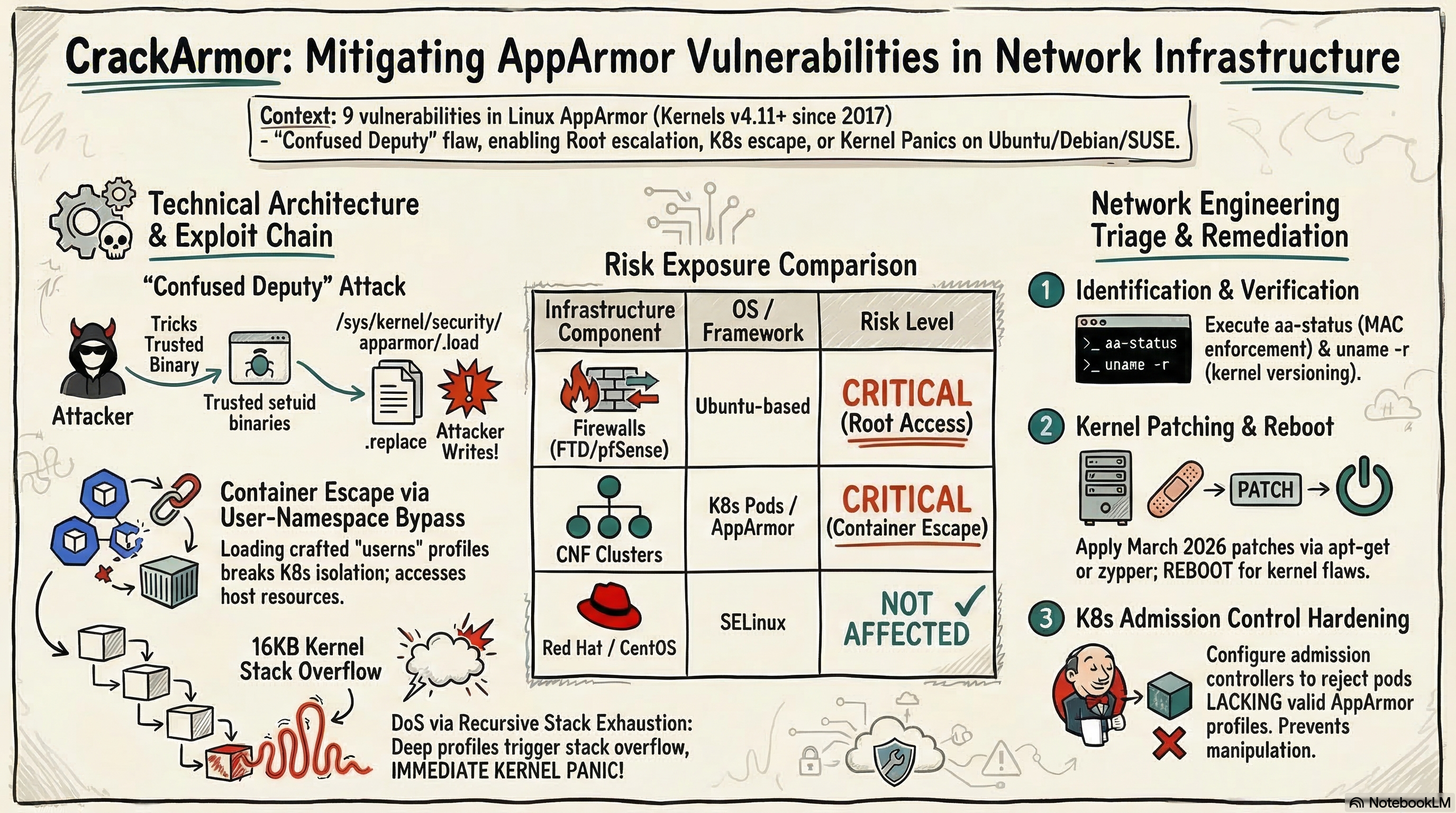
CrackArmor exploits a fundamental “confused deputy” problem in AppArmor’s kernel implementation. AppArmor is a Mandatory Access Control (MAC) framework that confines processes under security profiles — it’s been included in the mainline Linux kernel since version 2.6.36 (2010) and ships enabled by default on Ubuntu, Debian, and SUSE. The nine vulnerabilities allow an unprivileged attacker to trick privileged processes into performing actions they shouldn’t.
Here’s what the attack chain looks like in practice:
| Attack Vector | Mechanism | Impact |
|---|---|---|
| Profile manipulation | Write to pseudo-files /sys/kernel/security/apparmor/.load, .replace, .remove | Disable protections on any service |
| Privilege escalation | Leverage trusted tools (Sudo, Postfix) to modify AppArmor profiles | Full root access from unprivileged user |
| Container escape | Load “userns” profile to bypass user-namespace restrictions | Break container/Kubernetes isolation |
| Denial of service | Trigger recursive stack exhaustion via deeply nested profiles | Kernel panic and system reboot |
| KASLR bypass | Out-of-bounds read during profile parsing | Disclose kernel memory layout for further exploitation |
According to the Qualys technical advisory (2026), the analogy is straightforward: “This is comparable to an intruder convincing a building manager with master keys to open restricted vaults that the intruder cannot enter alone.” The attacker doesn’t need special permissions — they manipulate the privileged machinery that already exists.
Critically, as Qualys emphasizes, this is an implementation-specific flaw, not a failure of the MAC security model itself. AppArmor’s design is sound — the kernel module code that handles profile loading had specific bugs that went undetected for nine years.
Why Network Security Engineers Should Care — Right Now
AppArmor isn’t just an abstract Linux security feature. It’s the trust boundary for a massive amount of network infrastructure that security engineers manage daily.
Network appliances running Linux. Cisco’s Firepower Threat Defense (FTD), many next-gen firewalls, and several SDN controllers run on Linux-based operating systems. If your appliance vendor ships Ubuntu or Debian as the base OS with AppArmor enabled, CrackArmor applies to your network devices — not just your servers.
Containerized network functions (CNFs). The industry’s shift from hardware appliances to containerized network functions running on Kubernetes means AppArmor is often the primary security boundary between your network functions and the host OS. According to Kubernetes documentation (2026), AppArmor profiles are the recommended mechanism to “restrict a container’s access to resources.” CrackArmor breaks that restriction entirely.
NFV and edge deployments. Network Function Virtualization platforms running on Ubuntu or SUSE use AppArmor to isolate virtual network functions. A container escape in an NFV environment doesn’t just compromise one function — it can give an attacker access to the entire network control plane.
Jump boxes and management stations. If your network management infrastructure runs on affected Linux distributions, an attacker who gains unprivileged access to a management station could escalate to root and pivot into your network device management plane.
| Infrastructure Component | AppArmor Exposure | CrackArmor Risk Level |
|---|---|---|
| Linux-based firewalls (FTD, pfSense on Ubuntu) | Likely enabled by default | Critical — root = firewall control |
| Kubernetes CNF clusters | AppArmor profiles per pod | Critical — container escape |
| NFV platforms (SUSE, Ubuntu) | Default MAC enforcement | High — lateral movement to control plane |
| Network management stations | Varies by deployment | High — pivot to device management |
| Red Hat / CentOS devices | SELinux (not AppArmor) | Not affected |
How the Exploitation Chain Works: Technical Breakdown
For CCIE Security candidates and practicing network security engineers, understanding the exploitation mechanics matters because you’ll need to assess which of your infrastructure components are actually exploitable — not just theoretically vulnerable.
The Confused Deputy Attack
The core issue is that AppArmor allows unprivileged users to write to specific pseudo-files in /sys/kernel/security/apparmor/. Under normal operation, only privileged processes should modify these files. But the confused deputy flaw means an attacker can trick privileged tools that already have the necessary permissions into performing the writes.
Here’s the practical attack sequence:
- Attacker identifies a setuid binary (like
sudoorpostfix) that AppArmor trusts - Attacker crafts input that causes the trusted binary to write to AppArmor’s pseudo-files
- AppArmor profiles are modified — either disabled for a target service or replaced with a permissive profile
- Attacker exploits the now-unconfined service to escalate to root
Container Escape via User Namespace Bypass
This is particularly dangerous for network infrastructure. Ubuntu’s user-namespace restrictions were specifically designed to prevent unprivileged users from creating fully-capable namespaces. CrackArmor bypasses this by loading a specially crafted “userns” profile for /usr/bin/time, enabling the attacker to create namespaces with full capabilities.
In a Kubernetes environment running CNFs, this means:
- An attacker inside a containerized network function can escape to the host
- From the host, they can access other containers — including network controllers, routing daemons, and monitoring systems
- The Kubernetes AppArmor security boundary is effectively nullified
Denial of Service: Kernel Panic
The stack exhaustion vulnerability deserves attention from network operations teams. Deeply nested AppArmor profiles trigger recursive removal routines that can overflow the 16KB kernel stack on x86_64 systems. With CONFIG_VMAP_STACK guard pages (which most production kernels have), this triggers an immediate kernel panic and reboot.
For network infrastructure, an unexpected reboot of a firewall, router, or SDN controller is a production outage — and potentially a security gap during the reboot window.
Which Versions Are Affected and What’s the Patch Status?
Every Linux kernel since v4.11 (April 2017) is vulnerable on any distribution that integrates AppArmor. That’s nine years of exposure.
| Distribution | Affected? | Patch Status (March 2026) |
|---|---|---|
| Ubuntu (all supported releases) | Yes — AppArmor default | Patches available via apt |
| Debian (bookworm, trixie) | Yes — AppArmor default | Patches available via apt |
| SUSE / openSUSE | Yes — AppArmor default | Patches available via zypper |
| Red Hat / CentOS / Fedora | No — uses SELinux | Not affected |
| Alpine Linux | Varies | Check aa-status |
According to Canonical’s security advisory (2026), patched kernel versions include 6.8.x, 6.6.x LTS, 6.1.x LTS, and 5.15.x LTS. Your distribution’s specific package versions will vary — check your vendor’s advisory.
Important note on CVEs: As of this writing, no CVE identifiers have been assigned. According to Qualys (2026), the upstream kernel team typically assigns CVEs one to two weeks after fixes land in stable releases. Don’t wait for CVE numbers to justify emergency patching — the technical details and proof-of-concept code already exist.
Immediate Action Plan for Network Security Teams
Here’s your triage checklist, ordered by priority:
Step 1: Identify Affected Systems
# Check if AppArmor is loaded
aa-status 2>/dev/null && echo "AppArmor ACTIVE - check kernel version" || echo "AppArmor not active"
# Check kernel version (v4.11+ is vulnerable if AppArmor is active)
uname -r
Run this across your infrastructure — not just servers. Check your:
- Linux-based firewalls and security appliances
- Kubernetes nodes running containerized network functions
- NFV host systems
- Network management stations and jump boxes
- CI/CD systems that build or test network configurations
Step 2: Apply Kernel Patches
For Ubuntu/Debian systems:
sudo apt update && sudo apt upgrade -y linux-image-$(uname -r)
sudo reboot
For SUSE systems:
sudo zypper refresh && sudo zypper update kernel-default
sudo reboot
Schedule maintenance windows for network appliances. Yes, reboots are required — this is a kernel-level fix.
Step 3: Audit AppArmor Profile Integrity
After patching, verify that no profiles have been tampered with:
# List all loaded profiles and their enforcement mode
aa-status
# Check for unexpected profiles
ls /etc/apparmor.d/
# Verify no profiles were modified recently
find /etc/apparmor.d/ -mtime -7 -ls
Step 4: Harden Kubernetes AppArmor Enforcement
If you run containerized network functions on Kubernetes:
# Ensure AppArmor annotations are enforced, not just present
metadata:
annotations:
container.apparmor.security.beta.kubernetes.io/cnf-container: runtime/default
Verify that your admission controllers reject pods without AppArmor profiles — a post-patch hardening step that prevents future profile manipulation.
The Bigger Picture: Why MAC Vulnerabilities Matter for CCIE Security
CrackArmor is a textbook case of why the CCIE Security blueprint includes Linux security fundamentals. The exam expects you to understand how MAC frameworks like AppArmor and SELinux enforce policy — and how those policies can fail.
Three takeaways for your study and practice:
Defense in depth isn’t optional. AppArmor was one layer in a multi-layer security stack. When it failed, containers, user namespaces, and privilege boundaries all failed together. This is why zero trust architectures layer multiple independent controls.
Know your attack surface. CrackArmor is a local privilege escalation — it requires unprivileged access first. That means your network access controls, SSH hardening, and authentication policies are the first line of defense. If an attacker can’t get local access, CrackArmor is irrelevant.
Patch management is security engineering. As we covered in our Fortinet and Ivanti March 2026 CVE guide, the ability to rapidly identify, test, and deploy security patches across heterogeneous network infrastructure is a core competency — not an afterthought.
How CrackArmor Compares to Recent Network Security Vulnerabilities
To put CrackArmor in context with other recent vulnerabilities affecting network infrastructure:
| Vulnerability | Disclosure Date | Attack Vector | Impact | Patch Available |
|---|---|---|---|---|
| CrackArmor (AppArmor) | March 2026 | Local unprivileged | Root escalation, container escape | Yes (kernel update) |
| Fortinet FortiOS CVE-2025-24472 | March 2026 | Remote unauthenticated | Super-admin access | Yes (firmware update) |
| Ivanti Connect Secure CVE-2025-22467 | March 2026 | Authenticated remote | Remote code execution | Yes (firmware update) |
The key difference: CrackArmor requires local access, while the Fortinet and Ivanti vulnerabilities were remotely exploitable. But in environments where attackers already have a foothold — compromised containers, stolen SSH credentials, malicious insiders — CrackArmor turns limited access into total control.
Frequently Asked Questions
What are the CrackArmor vulnerabilities in Linux AppArmor?
CrackArmor is a set of nine vulnerabilities discovered by the Qualys Threat Research Unit in the Linux kernel’s AppArmor security module. They exploit a confused-deputy flaw that lets unprivileged users manipulate security profiles via pseudo-files, escalate privileges to root, break container isolation, and cause kernel panics. The flaws have existed since Linux kernel v4.11 (April 2017).
Which Linux distributions are affected by CrackArmor?
Any distribution that integrates AppArmor is affected, including Ubuntu, Debian, SUSE, and their derivatives. According to Qualys (2026), over 12.6 million enterprise Linux instances run with AppArmor enabled by default. Red Hat, CentOS, and Fedora are not affected because they use SELinux instead of AppArmor.
Do CrackArmor vulnerabilities affect network appliances and firewalls?
Yes — any network appliance, firewall, or security device running a Linux-based OS with AppArmor enabled is potentially affected. This includes Linux-based firewalls, NFV platforms, containerized network functions on Kubernetes, and network management stations. Check with your appliance vendor for specific advisories.
How do I check if my Linux system is vulnerable to CrackArmor?
Run aa-status to check if AppArmor is loaded and uname -r to verify your kernel version. If AppArmor is active and your kernel is v4.11 or later without March 2026 patches applied, your system is vulnerable. Check your distribution’s security advisory for the specific patched kernel version.
Have CVE identifiers been assigned for CrackArmor?
As of mid-March 2026, no CVE identifiers have been assigned. The upstream Linux kernel team typically assigns CVEs one to two weeks after fixes land in stable kernel releases. Qualys has published a full technical advisory and proof-of-concept details. Do not wait for CVE assignment before patching.
Ready to deepen your CCIE Security knowledge — including Linux security, MAC frameworks, and vulnerability management? Contact us on Telegram @phil66xx for a free assessment.